Hacking - A sophisticated threat to business
Unfortunately, a business was harmed in the making of this true story.
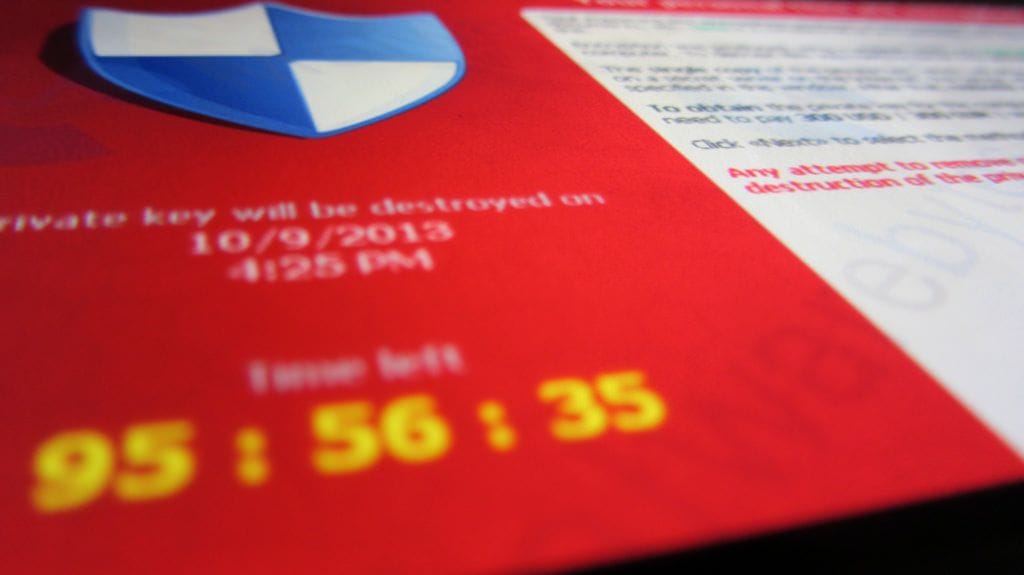
"Your files have been encrypted. Please submit payment within 48 hours to restore your data."

Can you imagine turning on your computer tomorrow and finding all of your business data inaccessible? Could you continue trading, or would your business come to a halt? This is the precise scenario a small business was recently faced with.
The business owners in this article, like many people, relished in the ability to complete work remotely from the comfort of home. But without the right security in place, their open connection to the network was like an unlocked door, and it was all too easy for hackers to gain access to the company's files.
So who are these hackers? Anyone with an internet connected computer is capable of attacking you. With anonymous cryptocurrencies and the ability to attack victims across the globe, cybercrime is virtually untraceable.
What are they after? Your data and information because it is not only extremely valuable to you, but is also a valuable commodity on the dark web. Your business data is like currency. Even in a small to medium business, data is just as attractive to hackers as a corner store cash register.
Hackers have two options with your data.
- They recognise that its worth more to you than it is to them, so they encrypt it (locking your files) and hold your business data for ransom-Usually this is referred to as Ransomware.
- They recognise that the data is valuable to them as well. Your customers' bank details, credit card numbers, and Medicare numbers fetch high prices when sold on the dark web. Once sold, such data is often used to commit identity fraud. A data breach like this could have a huge impact on the life of your clients.
The situation faced by the business I alluded to in the first paragraph is an example of how hackers make money from Ransomware. Through inadequate security measures, a hacker gained access to their server, encrypted all of their files, and then issued a ransom note for 0.8 Bitcoins (at time of attack - approximately A$7,500.00). The files were largely worthless to the hacker, BUT the files were the currency and life blood for the business. Bitcoin is a digital tender and can be used to buy and sell items anonymously on the internet meaning hackers have a way of being anonymously paid.
The challenge for any hacker is to gain access to your data storage (your laptop, server etc). There are many vectors for infection (the placing of malicious software in your system) and many methods where you can be tricked into letting the infection in including spam, social engineering and malicious advertising. Other ways that hackers can break in include website hacking and exploiting insecure remote access, insecure communications, aging equipment, and vulnerabilities in your software and/or equipment.
In the example of the Business mentioned earlier in this article, it was all too easy for a hacker to break in via the remote access.
But why this business? Well, it wasn't personal. It was simply a random leveraging of opportunity and high vulnerability increases opportunity. A hacker can go on any number of public websites that lists every device open to the internet and can apply his or her automation tools to choose targets to attempt to hack into. If you are reading this on your computer right now and you're online, your IP address is one of millions around the world that may come up in such a search.
Hackers utilise products such as Shodan (like a 'Google for hackers') and Masscan, meaning they can scan all four billion internet IP addresses, looking for vulnerabilities in less than six minutes. If a vulnerability or insecure practice is found, the hacker will look to leverage this into an attack. They don't necessarily know you, they just know your IP address is vulnerable and they will try to exploit it to see if they can earn some money.
Vulnerabilities are found in devices daily. They can take the shape of mistakes in programming, insecure policies by the device manufacturer or the deliberate inclusion of backdoor access in programming. But most vulnerabilities are just human error, with programmers often working under a lot of pressure to deliver a product this is why so many updates to Windows and Mac operating systems are pushed out each month.
So, the hackers have an easy way to scan the internet, they can access the known and published vulnerabilities, they have developed toolkits which will automate the entire process, they have tools to break in (a common example is automated password guessing-or brute force password hacking) and they can make untraceable money.
With these hacker strategies in mind, what happened with the small business in this article? The hackers, via their search engine and automation tools, were able to isolate a venerable IP address, which in this case it was the remote connection at the server. The hacker easily found their way to the server and started a brute force password attack. This sort of attack is not flagged by Windows and can only be determined by checking the event logs of the server. The hackers eventually guessed the right password which allowed them into the server. They deployed their ransomware software which encrypted all their data and then issued the ransom.
This catastrophe could have been avoided. If you are storing your data on a server at your business and accessing it remotely, there are three key ways to prevent hacking.
- Set up a secure remote connection to the business via a Virtual Private Network (VPN) appliance.
- Have a bulletproof backup solution in place that follows the 3-2-1 backup framework.
- Have a strong password management regime.
Without the VPN, a remote connection opens a portal into your server that is visible and easily accessed by anyone else. A VPN reduces the 'visibility' of the remote connection and provides the security to prevent any unauthorised entry.
If the business in this article had a bullet proof 3-2-1 back-up solution in place; then at least they could have ignored the ransom, purged the server, installed the necessary VPN and endpoint security and then loaded their back-up data.
Lastly, with an appropriate password management regime, maybe the hackers would not have been able to crack this Business's password.
So, how did this story end for the Business in this article? Not too well I am afraid. The ransom was paid but then the hackers went quiet. There has been no contact since. They did not deliver the decryption key nor the program to decrypt the data. They had to downsize their operation significantly.
The moral to this story is this: regular security audits should be implemented on business networks to ensure best practices are being adhered to and when issues are found, it is always best to action them with urgency.
Download our Insight Feature on Hacking - A Sophisticated Threat to Business
You may also like to read these fact sheets:
) Author:Michael Trimblett
Author:Michael Trimblett| Tags:ITSecurityNetworking SecurityIT Consulting |
&geometry(115x98))